Certifications, standards posture, and trust documents.
This page lists what AmbiSecure is actively certified for, the standards we build against, certifications that are targeted for upcoming product tiers, and the trust documents we maintain. We are conservative in what we claim — if a certificate is in flight rather than awarded, we say so.
Last reviewed: 2026-05-09. For the most up-to-date status of any specific certification, talk to our engineering team.
What we are actively certified for
Listed verbatim from public AmbiSecure communications. Independently verifiable via the relevant standards body where applicable.
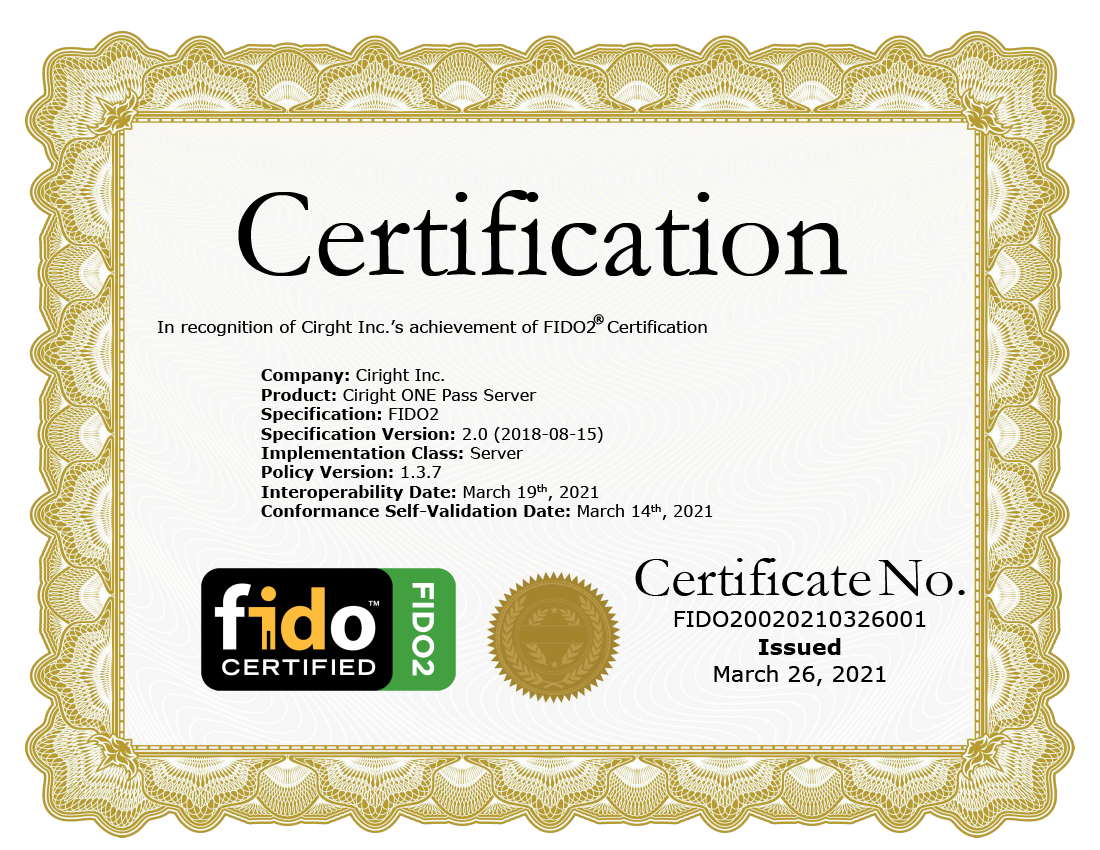
| FIDO Alliance — FIDO Certified products |
Legacy claim, preserved as-is: "AmbiSecure products are a FIDO certified."
Specific certified product SKUs and FIDO Certified levels can be verified through the FIDO Alliance public certified products listing at fidoalliance.org/certification/fido-certified-products/. Status: Active. Certificate IDs and FIDO Certified levels supplied on request under NDA, then independently verifiable on the FIDO Alliance site. |
|---|---|
| FIDO Alliance membership |
AmbiSecure (Ambimat Electronics) participates in the FIDO Alliance ecosystem and ships products under the FIDO U2F (CTAP1) and FIDO2 (CTAP2 / WebAuthn) protocols.
Status: Active. |
Conformance marks and trust references
Conformance marks carried on AmbiSecure product communications. Validity of any third-party mark is verifiable on the issuing organisation’s site.


Standards we build against
These are not certifications — they are the specifications our products implement. Conformance is verifiable through inspection of the public protocol output (APDUs, CTAP frames, BER-TLV, etc.); see our utility tools.
| Authentication | FIDO U2F (CTAP1); FIDO2 (CTAP2.1); W3C WebAuthn Level 2; COSE (RFC 8152); CBOR (RFC 8949) |
|---|---|
| Identity | NIST SP 800-73 PIV (parts 1–4); RFC 4880 OpenPGP card spec |
| Smart card / contactless | ISO/IEC 7810 ID-1; ISO/IEC 7816-3/4; ISO/IEC 14443 Type A; ISO/IEC 8825 BER/DER |
| Card OS | JavaCard 3.x; GlobalPlatform 2.3.1 with Amendment D SCP03 |
| Cryptography | NIST FIPS 186-4 (DSA/ECDSA); NIST SP 800-38B (CMAC); FIPS 197 (AES); RFC 5869 (HKDF) |
| eSIM | GSMA SGP.22 (consumer eSIM); GSMA SGP.32 (M2M eSIM); ETSI TS 102 221 |
| NFC | NFC Forum NDEF 1.0; NFC Forum Type 4 Tag |
| PKI | X.509 v3 (RFC 5280); PKCS#10; PKCS#11 v2.40; PKCS#12; PKCS#15 |
| Identity assurance | NIST SP 800-63-3 AAL3 architecture patterns |
Certifications we are targeting
These are explicit certification targets for current and upcoming product tiers, not active certifications. Each is being pursued in collaboration with the relevant chip vendor or accredited lab.
| FIDO Certified Level 1 | Targeted across the OnePass authenticator family (Card, USB Key, BioKey, Tappable). Status: in evaluation pipeline. Verifiable on award via fidoalliance.org. |
|---|---|
| FIDO Biometric Component | Targeted for OnePass Bio Card and BioKey. Match-on-card / match-on-device evaluation path. |
| Common Criteria EAL5+ chip platform | Our reference secure-element silicon partners hold CC EAL5+ chip-platform certificates. AmbiSecure applets layered on those platforms inherit the chip-level evaluation; the applet layer itself is not separately CC-evaluated by default. |
| SSCD / QSCD evaluation | Targeted for the Digital Signature Token under specific customer roadmaps (eIDAS-aligned issuance). |
No claim of active certification at the AmbiSecure product / applet layer is implied for any of the above unless explicitly listed in the "Active" section.
Compliance frameworks we support
These are frameworks our products are designed to fit inside — not certifications we hold. Customers may pursue accreditation against these frameworks using AmbiSecure components as building blocks.
| NIST SP 800-63-3 | AAL3 architectures using AmbiSecure FIDO + biometric authenticators. |
|---|---|
| OMB M-22-09 | Phishing-resistant MFA for U.S. federal civilian executive-branch deployments. |
| eIDAS | Qualified electronic signatures — achievable via AmbiSecure Digital Signature Token paired with a Qualified Trust Service Provider. |
| EU Cyber Resilience Act (CRA) | IoT product cyber-resilience baselines — supported via AmbiSecure IoT Security Chipset and IoT Solution. |
| GSMA SAS-UP / SAS-SM | Subscriber-management security accreditation — supported through Ambimat’s eSIM Initiative line at esim.ambimat.com. |
Trust documents on request
The following documents are made available under NDA during procurement. Public-facing copies are deliberately not posted because most carry chip-vendor-confidential information. Email support@ambimat.com with your engagement scope.
- Per-product datasheet (security model, applet matrix, certification status)
- Personalisation-line audit hooks and chain-of-custody description
- SCP03 / GlobalPlatform key-ceremony procedure
- Secure-element chip-platform CC EAL certificate (issued to the silicon vendor; provided as a reference document)
- FIDO Certified product certificate IDs (independently verifiable on the FIDO Alliance site once disclosed)
- Standard-form vendor-security-questionnaire responses (CSA STAR-style)
What this page is and is not
- This page is not a certificate. It is a summary of certification posture. Active certificates and certificate IDs are issued by independent bodies and are verifiable on those bodies’ sites — not on ours.
- Standards conformance is not certification. Building to a standard (e.g. ISO/IEC 7816-4) is not the same as being certified against an evaluation scheme. We list the two separately.
- Chip-level evaluation does not auto-extend to the applet layer. A CC EAL5+ chip-platform certificate is held by the silicon vendor and applies to the chip platform; AmbiSecure-authored applets sitting on that platform are not separately evaluated unless explicitly stated.
- "Targeted" means in flight, not awarded. Targets in the evaluation pipeline are clearly marked as such.
- Legacy badge artwork is reproduced as-is. Continued validity of any third-party trust mark should be verified with the issuing organisation.
- Compliance frameworks are deployment patterns, not held accreditations. Customers can pursue accreditation against these frameworks using AmbiSecure components; AmbiSecure itself does not claim those accreditations except where explicitly listed in the "Active" section above.
Need a specific certificate document for procurement?
Tell us which product, which framework, and which evaluator. We will send you the active certificate IDs (verifiable on the issuing body’s site) and any reference documents that are appropriate to share at your stage of engagement.