Hardware-rooted security engineers.
The security business unit of Ambimat Electronics — an embedded engineering team shipping electronics since 1981 and identity systems since 2017.
 Identity infrastructure for connected systems
Identity infrastructure for connected systems
FIDO authenticators, PIV applets, PKI infrastructure, JavaCard platforms, Secure Elements, ePassport systems, and IoT trust anchors — engineered for governments, enterprises, telecoms, and connected-product OEMs.

The security business unit of Ambimat Electronics — an embedded engineering team shipping electronics since 1981 and identity systems since 2017.
FIDO2 authenticators, JavaCard applets, ePassport platforms, IoT trust anchors, and validation servers — rooted in CC EAL5+ silicon.
National identity programmes, enterprise IT, telecom operators, transit authorities, connected-product OEMs, and security integrators.
Silicon selection, applet engineering, personalisation lines, form-factor delivery, and validation servers — scoped as review, pilot, or rollout.
FIDO2, PIV, OpenID Connect, and IoT-identity applets ship on the same CC EAL5+ secure-element silicon in two packages: a nano-card form factor for issuance and handling, and a solderable MFF2 module for embedding directly into connected-product boards. Same applet code, same certifications, same personalisation pipeline.
Secure-element integration, V2X PKI architecture, and OBU/RSU hardware identity for ITS.
Authenticators, validation server, attestation, MDS — with a public utility-tool surface.
Custom applets, CAP file delivery, SCP03 loading, JCOP 3.1, JavaCard 3.x.
EV1 / EV2 / EV3, SAM-backed offline trust, low-latency fare validators.
Hardware-protected signing keys, PKCS#11, eIDAS-compatible flows, audit-grade issuance.
CC EAL5+ silicon, attestation, key rotation, signed update — the foundation beneath every pillar.
SGP.22 / SGP.32 eUICC platform, OpenID Connect applet, automotive + M2M variants.
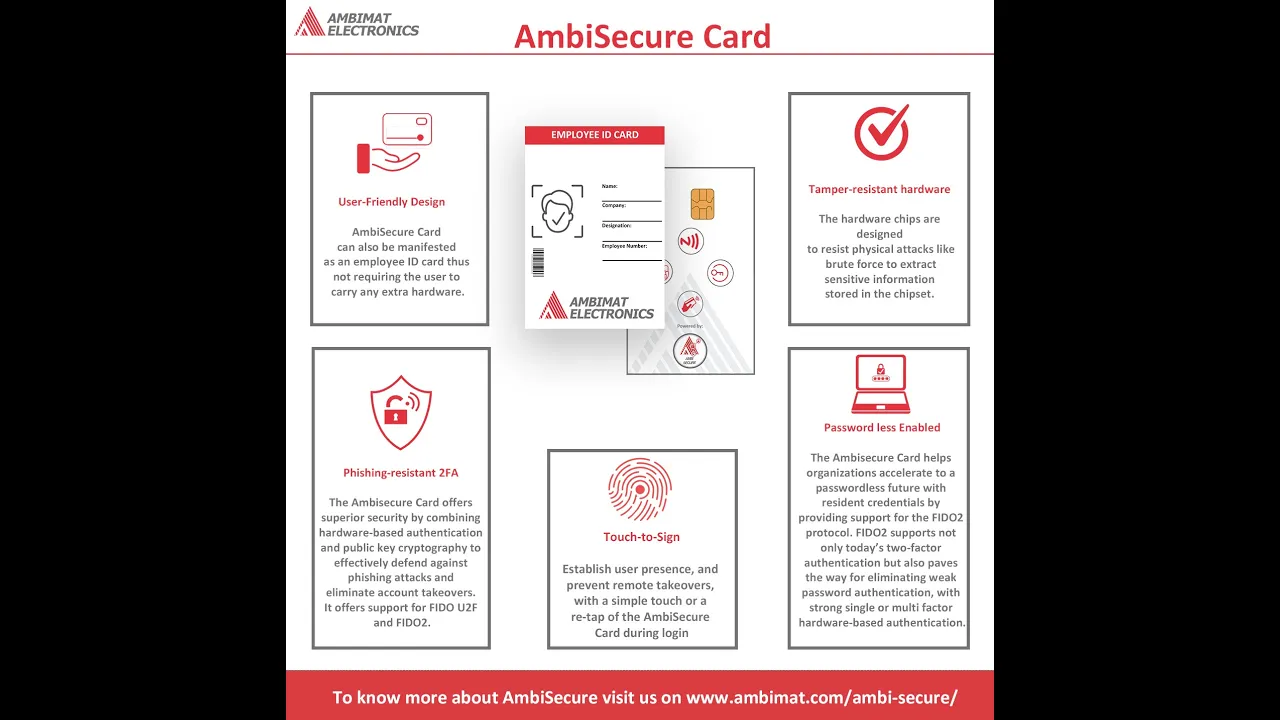
The flagship product family — Card, Bio Card, USB Key, BioKey, and Tappable.
Every product and service plugs into the same architecture — identity that begins in silicon and travels intact to the application layer.
OnePass Card, Bio Card, USB Key, BioKey, Tappable — FIDO2 / U2F, hardware-bound credentials, no shared secrets.
FIDO, PIV, OpenPGP and custom applets — designed, written, loaded, and personalised on chips at scale.
Dual-domain co-processor — the MCU runs the application while the cryptographic domain holds keys, verifies OTA, and anti-replays. Identity below the firmware.
Multi-tenant FIDO2 / WebAuthn SaaS. Per-tenant policy, attestation verification, MDS lookup. Drop-in JS + tenant-scoped REST.
End-to-end ICAO 9303 platform — backend, frontend, CSCA / DSC / PKD PKI, enrolment, personalisation.
Telecom-grade embedded identity, eSIM/eUICC architecture, profile lifecycle — explored on our dedicated SIMAuth site.
Software-only security inherits every weakness of the host. We anchor trust in a tamper-resistant Secure Element, then carry it up through firmware, OS, and application boundaries with verifiable transitions.
Replace shared-secret passwords with hardware-bound FIDO2 credentials. Phishing-resistant by construction.
Adding a secure element to a connected-device BOM — from silicon selection to SMT-line personalisation.
Personalisation lines for cards and devices — key splits, HSM-backed custody, audit trails, batch APDUs.
PIV, OpenPGP, and eID applets on smart cards and tokens — issuance and revocation that holds up to audit.
SAM-backed transit and access systems with offline trust and audit-grade tap journals.
Reader-and-SAM platforms for fare collection and access — built to keep working when the backend doesn’t.
Four ways into the same trust chain — by product, by audience, by standard, or by stack layer.
Cards, USB keys, biometric tokens, secure-element applets, IoT applets, signature suites — all the hardware AmbiSecure ships.
JavaCard development, FIDO validation server, tool-chain engineering, ePassport platform — engineering work AmbiSecure does directly.
Passwordless workforce, closed-loop transit, government identity, IoT trust, phishing-resistant MFA — problem-shaped views.
FIDO2, WebAuthn, CTAP2, passkeys, JavaCard, DESFire, secure elements, SAMs, attestation — the standards layer.
Government, enterprise IT, transit, IoT/industrial, telecom — vertical-specific deployment shapes and constraints.
AAGUIDs, APDU status, ASN.1, ISO 7816, COSE, X.509, GlobalPlatform, EMV, NFC, CAP files, DESFire — searchable databases.
54 client-side utilities for parsing, decoding, building, and signing — the engineer’s toolbox.
21 modern engineering deep-dives plus 24 archived posts — cornerstone reading on FIDO, JavaCard, PKI, transit, IoT.
Free, client-side utilities for parsing the hex you stare at every day. Nothing leaves your browser. No accounts, no ads.
Decode Answer-To-Reset bytes — TS, T0, interface bytes, historical bytes, TCK.
Decode CLA / INS / P1 / P2 / Lc / Le for Case 1–4, short and extended.
Walk BER-TLV, EMV TLV, and DGI-TLV trees with tag dictionary lookup.
Utilities for ASN.1, CBOR, COSE, AAGUID, X.509, SCP03, NDEF, DESFire, EMV, and more.
AmbiSecure is the security business unit of Ambimat Electronics — established 1981. We have shipped firmware, contactless modules, and GSM/Bluetooth platforms for medical devices, wearables, and utilities. Security is engineered into that DNA, not layered over someone else’s reference design.
A walkthrough of the FIDO2 stack — CTAP2, WebAuthn, attestation — with code that compiles.
Read → MFACybercriminals have billions of leaked records. Why a second factor — especially a hardware-bound one — cuts off the long tail.
Read → MFAThe three reasons MFA isn’t optional any more — and what changes when the second factor is hardware.
Read →FIDO setup walkthroughs, multi-application card use cases, and product loops — under 90 seconds each.
FIDO, PIV, door access, NDEF, and OpenPGP roles on a single multi-application card.
View page →
Adding the card as a FIDO security key on a Google account, on desktop.
View page →Short hero loop showing the biometric USB security key.
View page →AmbiSecure sits between the silicon vendor and the application developer — picking the chip, writing the applet, running personalisation, shipping the authenticator, and standing up the validation server. Steps that are usually each their own RFP.
CC EAL5+ secure element from a partner vendor.
FIDO, PIV, OpenPGP, NDEF, OIDC, IoT — AID-selectable on one chip.
SCP03 loading, per-card key derivation, AAGUID + attestation cert injection.
Card, USB key, biometric variant, NFC fob — brandable.
FIDO Validation Server with REST + JS API — or your own RP.
Certification posture, standards conformance, security model, and vulnerability disclosure.
What we are certified for, the standards we build to, and what we are targeting — with explicit disclaimers.
Resellers, OEMs, system integrators, MSSPs, and consultancies — the partner programme front door.
Evaluating whether AmbiSecure fits your deployment? These three surfaces are the most useful next step — architecture studies, platform overviews, and engagement-model shapes.
Three anonymised deployments — passwordless workforce, closed-loop transit ticketing, IoT device identity. Architecture-led.
Six platform overviews — OnePass, FIDO, transit, JavaCard, PKI, device identity. Printable, no lead-capture wall.
How engagements are scoped — architecture review, pilot, rollout, integration, secure manufacturing, custom JavaCard.
Hardware-rooted identity systems — FIDO2 authenticators, PIV smart cards, JavaCard applets, ePassport platforms, eSIM and secure-element authentication, PKI, and IoT trust anchors — for governments, enterprises, telecoms, and connected-product OEMs.
Both, by design. AmbiSecure ships JavaCard applets, FIDO Validation Server software, and tool-chains on top of certified secure-element silicon. The promise is wafer-to-validation in one engineering team rather than three vendor handoffs.
FIDO2 / WebAuthn / CTAP2, PIV / FIPS 201, JavaCard 3.x with GlobalPlatform and SCP03, IEEE 1609.2 for V2X PKI, GSMA SGP.22 / SGP.32 for eSIM, ICAO 9303 for ePassport, and CC EAL5+ secure-element silicon. Posture is documented on the trust center.
Engineering and procurement teams that need device-bound rather than syncable identity — connected-mobility OEMs, transit operators, government identity programmes, telecom eSIM rollouts, and security leads who evaluate against threat models rather than feature lists.
Most start as “we need something like X but with Y.” Tell AmbiSecure about the Y — there is usually an applet, a tool, or a secure-element pairing that gets you most of the way there. See the engagement models for the usual shapes.
Talk to engineers, not BDRs. Tell us what you are building and we will tell you what is realistic, standards-aware, and shipped before.